How Passwordless Authentication Mitigates Password Spraying

Passwordless authentication mitigates password spraying attacks by eliminating the need for users to remember and input passwords. Instead of relying on traditional username-password combinations, passwordless authentication typically employs alternative methods such as biometrics (e.g., fingerprint or facial recognition), hardware tokens, one-time passcodes (OTPs) sent via email or SMS, or cryptographic keys.
Understanding Password Spraying Attacks:
- Definition: Password spraying attacks involve systematically attempting a few commonly used passwords against a large number of accounts to gain unauthorised access.
- Methodology: Instead of targeting a single account with multiple password attempts (brute force), attackers cast a wide net, making detection and prevention challenging.
- Impact: Successful password spraying attacks can lead to unauthorised access to sensitive information, financial loss, reputational damage, and regulatory penalties.
Here’s how passwordless authentication helps mitigate password spraying attacks:
- No Passwords to Guess: In a password spraying attack, the attacker tries a few commonly used passwords against many accounts. With passwordless authentication, there are no passwords to guess, making such attacks ineffective.
- Stronger Authentication Methods: Passwordless authentication often employs more robust and multifactor authentication methods. For instance, biometric authentication or cryptographic keys offer stronger security compared to traditional passwords, making it harder for attackers to compromise accounts.
- Reduced Credential Exposure:Since users don’t need to enter passwords, there’s no risk of them accidentally exposing their credentials through phishing or other social engineering attacks. Passwordless methods like OTPs or cryptographic keys are usually transmitted securely and are less prone to interception.
- Limited Attack Surface: Passwordless authentication systems typically have a smaller attack surface compared to traditional password-based systems. For example, biometric authentication relies on physical traits that are difficult to replicate, reducing the likelihood of successful attacks.
- Dynamic and Time-bound Tokens: Some passwordless authentication methods, such as OTPs, are dynamically generated and have a limited lifespan. This makes it challenging for attackers to reuse intercepted credentials or launch prolonged attacks.
- Continuous Authentication: Some passwordless systems support continuous authentication, where the user’s identity is continuously verified based on their behaviour patterns or biometric data throughout the session. This further enhances security by reducing the risk of unauthorised access even if initial authentication is compromised.
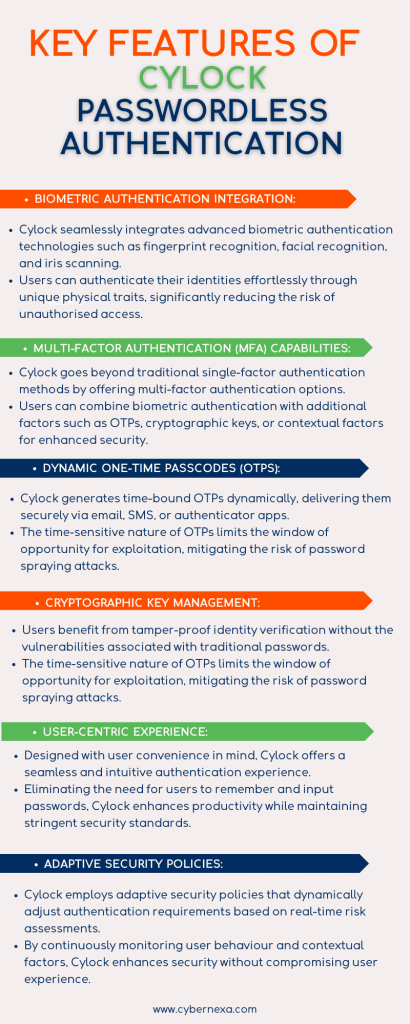
Introducing Cylock Passwordless Authentication:
In response to the growing challenges posed by traditional password-based authentication methods and the increasing sophistication of cyber threats, Cylock Passwordless Authentication emerges as an innovative solution to secure digital identities while enhancing user convenience. Developed by leading cybersecurity experts, Cylock represents a paradigm shift in authentication mechanisms, offering a robust defence against password spraying attacks and other common vulnerabilities associated with traditional passwords.
Advantages of Cylock Passwordless Authentication:
- Enhanced Security: Cylock mitigates the risk of password spraying attacks and other common vulnerabilities associated with traditional passwords, offering robust protection for digital identities.
- User Convenience: By eliminating the need for users to remember and input passwords, Cylock streamlines the authentication process, enhancing user productivity and satisfaction.
- Compliance and Regulation: Cylock helps organisations meet regulatory requirements and industry standards by implementing advanced authentication mechanisms and ensuring data security and privacy.
- Low Total Cost of Ownership (TCO): Cylock’s efficient authentication process reduces the administrative burden associated with password management, leading to lower operational costs over time. Additionally, the avoidance of potential data breaches and associated costs further contributes to a reduced TCO.
- Scalability and Integration: Cylock is scalable and can be seamlessly integrated with existing IT infrastructure, allowing organisations to adapt to evolving security needs and technological advancements.
Conclusion:
In an era defined by increasing cyber threats and the imperative for enhanced digital security, Cylock Passwordless Authentication emerges as a transformative solution that combines cutting-edge technologies with user-centric design principles. By offering advanced biometric authentication, multi-factor authentication capabilities, dynamic OTP generation, cryptographic key management, adaptive security policies, and a low total cost of ownership, Cylock sets a new standard for authentication mechanisms, empowering organisations to safeguard their digital assets while delivering a seamless user experience.







